Imagine you found the perfect plugin for your WordPress website. It has all the bells and whistles — and you can’t wait to see how it boosts your website.
Excited to try it out, you quickly download and install it.
Within hours, your website’s load time doubles, your analytics program reports suspicious traffic, and spam floods your email inbox.
Unfortunately, this nightmare scenario is more common than you might think. But with countless WordPress plugins available, how can you determine which are unsafe?
Keep reading to find out.
- Not all WordPress plugins are safe
- How to check if a WordPress plugin is safe
- Common plugin red flags to look out for
- Final thoughts: How to check if a WordPress plugin is safe or not (full guide)
Get fully managed WordPress hosting
Power your site with the industry's most optimized WordPress hosting
Not all WordPress plugins are safe
With WordPress powering a staggering 43% of all websites on the internet, it's no surprise that it’s a prime target for hackers and cybercriminals.
One reason for the popularity of WordPress is its vast library of free plugins. At the time of writing, WordPress users can access over 60,000 plugins.
Many WordPress plugins get created by reputable developers. They undergo security checks and have active installations.
But others aren’t. They might be poorly coded or even intentionally malicious.
Malicious code can lead to plugin vulnerabilities in your website. It exposes your website to attacks, slow performance, and other issues.
To protect your website, you need to discern which plugins are safe — and which aren’t.
How to check if a WordPress plugin is safe
Your online presence is important no matter how large your business is. And if your WordPress site experiences downtime, it could be costly for your company. Not to mention, it could hurt your reputation with customers.
Avoiding vulnerable plugins is one way you can help prevent downtime and other pricey problems. Here’s how you can check if a WordPress plugin is safe or has security vulnerabilities.
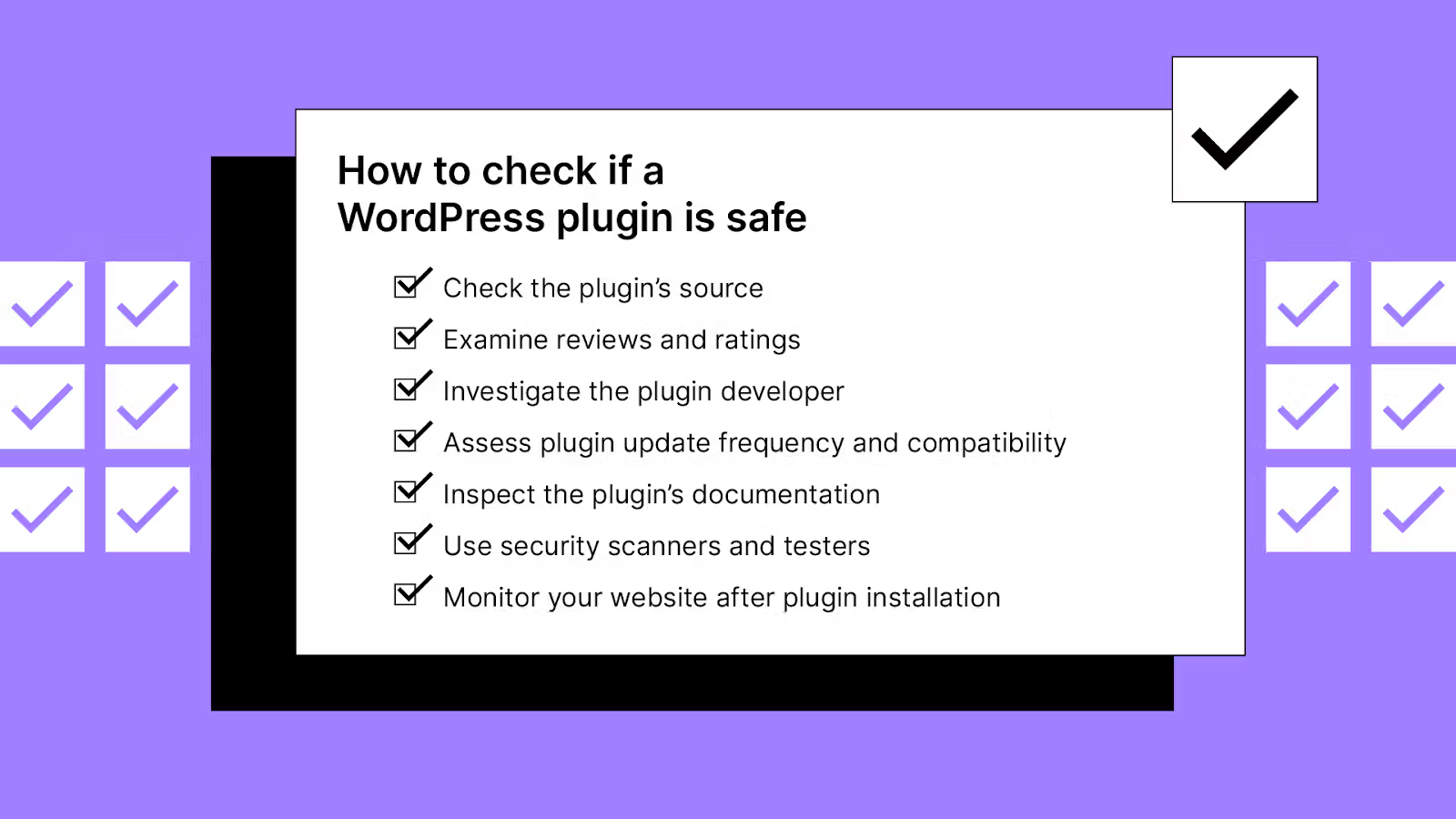
Check the plugin’s source
The plugin’s source is where you plan to download it. The official WordPress Plugin Repository is the safest and most reliable plugin source. Each new plugin submitted to the marketplace undergoes a review process to ensure it meets quality standards.
While third-party websites also offer plugins, they might be unsafe, exposing you to potential risks.
Examine reviews and ratings
Reading reviews and ratings for a WordPress plugin can provide insights into its performance, security, and overall quality. Users who have encountered problems or issues with a plugin will likely share their experiences in reviews.
Here’s what to look for in plugin reviews.
- Total number of reviews: A high number of reviews can indicate a good plugin. However, it’s always a good idea to read some to confirm. Also, check third-party sources to verify the reviews are legitimate.
- Average rating: An average rating above four stars is ideal, showing most users have had a positive experience with the plugin.
- Recent reviews: Recent reviews confirm the installed plugins still function well and aren’t compromised. Also, they’ll give insight into whether the plugin is maintained.
- Common issues: Before downloading, take a look at the negative reviews. Do they share anything in common, and would they apply to you? Understanding potential problems allows you to avoid frustration and keep your website secure.
Look for a combination of positive factors and weigh them against any negatives. For instance, if a plugin has a high number of reviews but they’re all old, you should consider alternatives.
We’ll go over the red flags to look for later in the article.
Investigate the plugin developer
A reputable developer is more likely to maintain high-quality, secure plugins and provide necessary updates and support.
Start by visiting the developer's website to learn more about their background, expertise, and other products they offer. A professional website with detailed information shows the developer takes their work seriously.
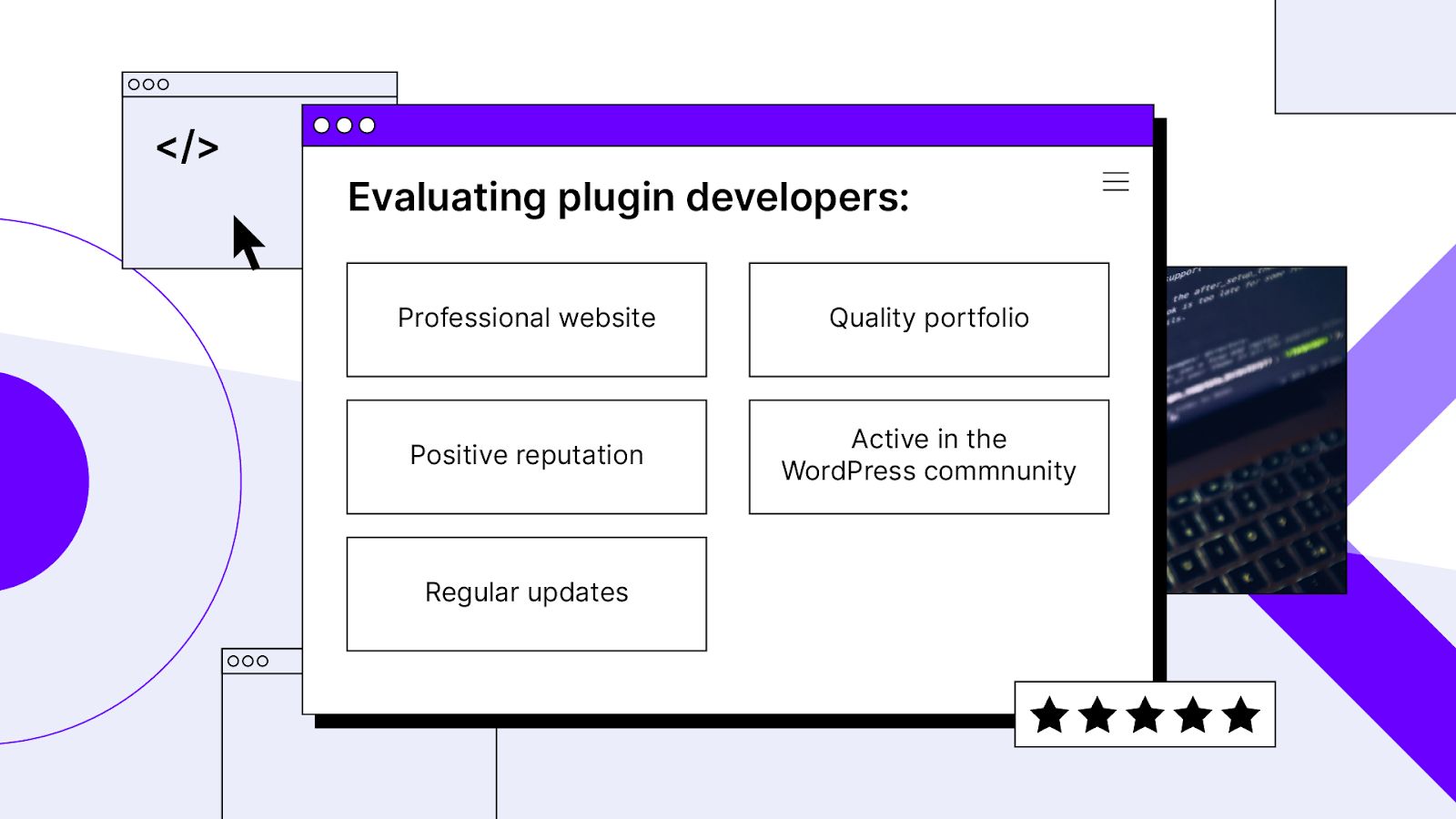
Checking the plugin's changelog or update history can also provide valuable insight. Frequent updates and improvements show that the developer actively maintains their plugin and addresses any issues.
And if the developer is active in the forums, you can bet they're committed to providing a great product.
Assess plugin update frequency and compatibility
A regularly updated plugin has less risk of WordPress security issues. If the developer hasn’t updated the plugin in a long time, it could signal that they no longer actively support it. And using an unsupported plugin might leave your website at risk.
Also, check the plugin’s compatibility with your current version of WordPress. Incompatible plugins can cause conflicts or unexpected behaviors on your website. Most developers will list the compatible WordPress versions in the plugin's description or documentation.
Inspect the plugin’s documentation
Whether it’s a user manual or a simple website with tips, a plugin’s documentation or tutorial can save you several hours. It’s a sign the developer cares for both the users and the product.
If documentation is available, take some time to read it. It can help you avoid any hassles or surprises with how your plugin works down the road.
Use security scanners and testers
Security scanners allow you to verify the safety of plugins before installing them. Some popular tools include Solid Security Pro, WPScan – Plugin Security Scanner, and Jetpack Protect.
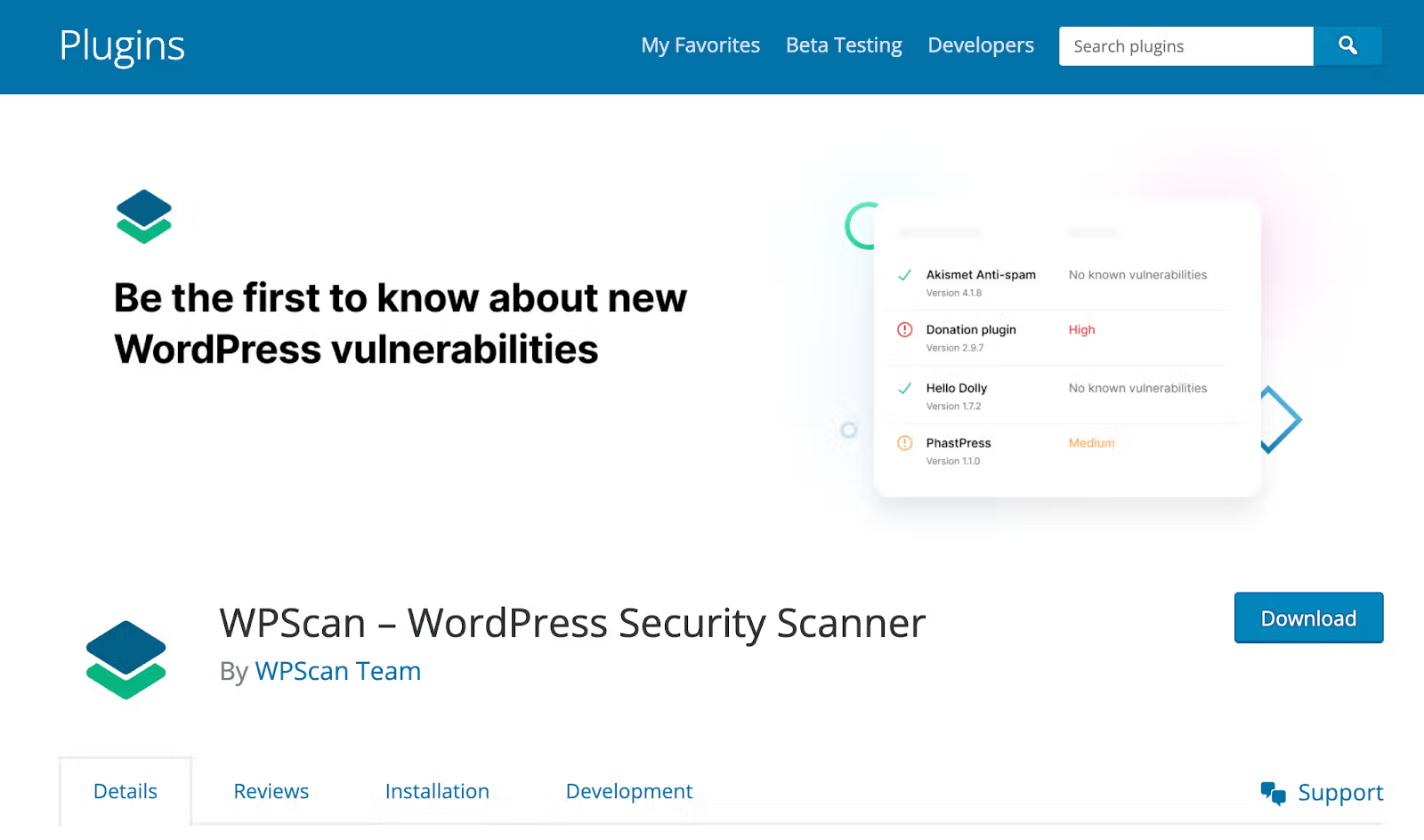
Using these tools, you can proactively identify potential problems and make an informed decision about installing a particular plugin.
Monitor your website after plugin installation
After taking all the necessary precautions, it’s wise to watch your website’s performance and status. Monitor your website's load times, analytics data, and error logs for unusual behavior or potential issues.
You also can use a security plugin like Wordfence or Sucuri to help protect your website from potential threats. These tools can identify and block malicious traffic, scan for vulnerabilities, and alert you to website security issues.
If you want, you can set up notifications and automatic updates to ensure you handle issues promptly.
Common plugin red flags to look out for
Now that we’ve covered the green flags for plugins, let’s look at the red flags.
Note: Look for multiple red flags to determine a plugin’s legitimacy. One red flag won’t always mean a plugin is insecure. But two or three might indicate threats like malware.
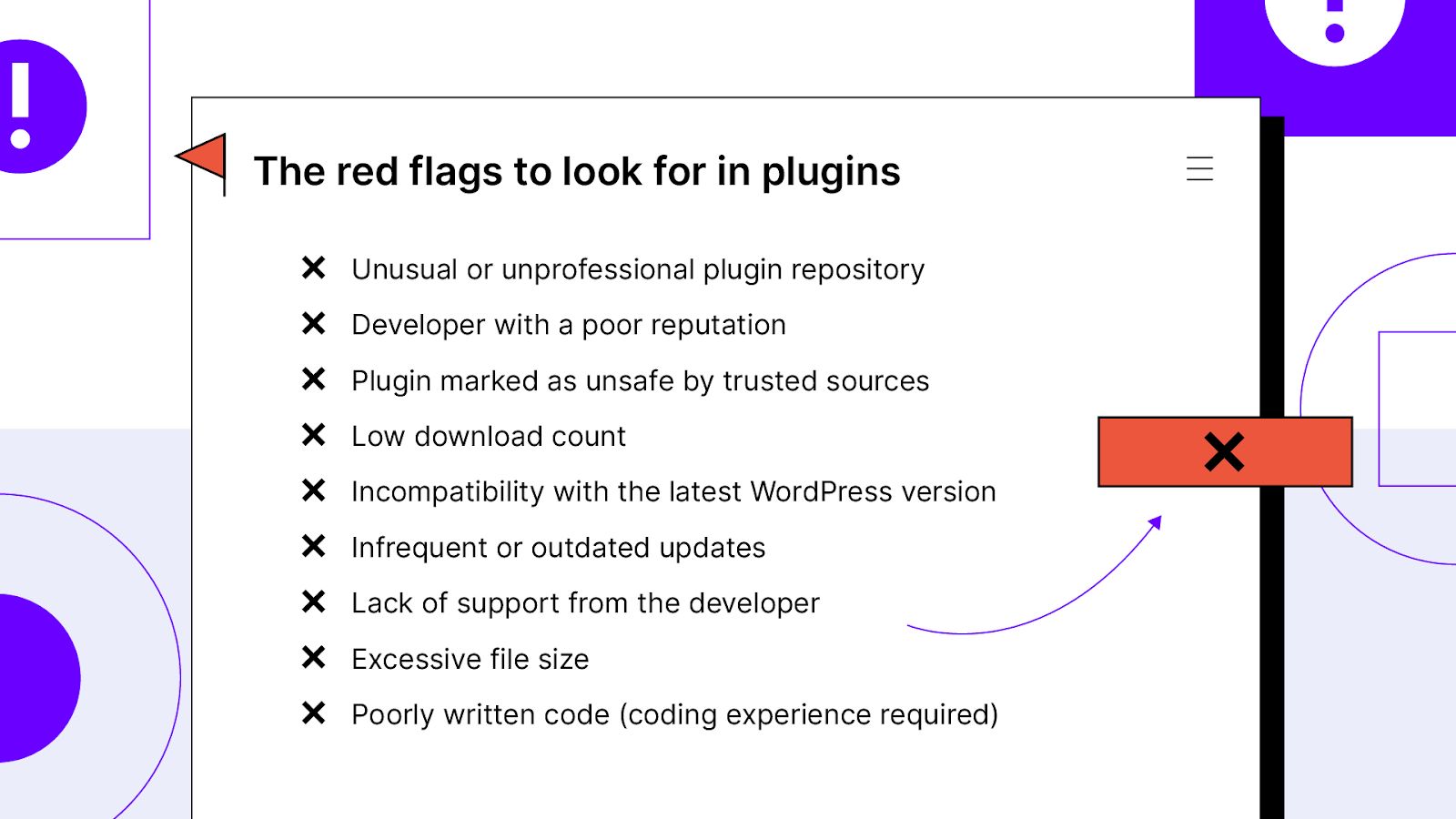
Unusual or unprofessional plugin repository
Be cautious of plugins found on a suspicious or unprofessional repository. They may not have undergone thorough vetting for security and quality standards.
If possible, stick to WordPress.org when searching for plugins.
Developer with a poor reputation
When comparing your options, opt for the plugin from an experienced, high-quality developer. Plugins from low-quality developers could be less secure. User reviews, a quick Google search, and the developer’s website are good places to learn more.
Plugin marked as unsafe by trusted sources
If reliable sources flag a plugin as dangerous, it's wise to avoid it. You can check the WPScan Vulnerability Database or well-established blogs.
Low download count
A plugin with a low download count may not be widely adopted. That could point to quality, performance, or security issues that deter users from installing it. But consider comparing it with other options before making a final decision.

Incompatibility with the latest WordPress version
Another red flag is if a plugin hasn't been updated to work with the latest version of WordPress. Using it could lead to security risks. The plugin could also have issues working with other parts of your website, like your WordPress theme or other plugins.
Infrequent or outdated updates
A plugin with a sparse update history or long gaps between updates might suggest that the developer no longer actively supports it. Using it could leave your website vulnerable to security threats and compatibility issues.
Lack of support from the developer
Check to see if the plugin developer actively participates in forums, responds to user inquiries, or addresses concerns. If they don’t, it may indicate that they aren’t committed to maintaining the plugin. A poorly maintained plugin could have security flaws or compatibility problems.
Excessive file size
A plugin with an unusually large file size could consume excessive server resources. It may indicate poor optimization or hidden malicious functions.
Poorly written code (coding experience required)
If the plugin's code appears suspicious, poorly written, or difficult to understand, it could indicate potential security risks or hidden malicious functions. You’ll need to know how to code to identify this red flag. The programming languages you’d need to understand include PHP, SQL, CSS, HTML, and JavaScript.
Final thoughts: How to check if a WordPress plugin is safe or not (full guide)
While the WordPress community is filled with experienced, supportive developers, bad apples still exist. By using these checklists to evaluate potential plugins, you can avoid security, performance, and user experience issues.
Don’t want to be responsible for regularly updating your website? Protect yourself with fully managed WordPress hosting solutions from Nexcess. With our top-notch customer support, lightning-fast hosting, and plugin monitoring service, you can rest assured your website will run smoothly.
Check out our managed WordPress plans today.